DCMM Security and Automation
As businesses evolve and technological advancements accelerate, DCMM (Data-Centric Modernization and Migration) security and automation become increasingly indispensable. If youre pondering over the necessity of DCMM for your organization, lets dive deep into how these processes are essential and how they intertwine with tools offered by Solix Technologies, enhancing your data management practices effectively.
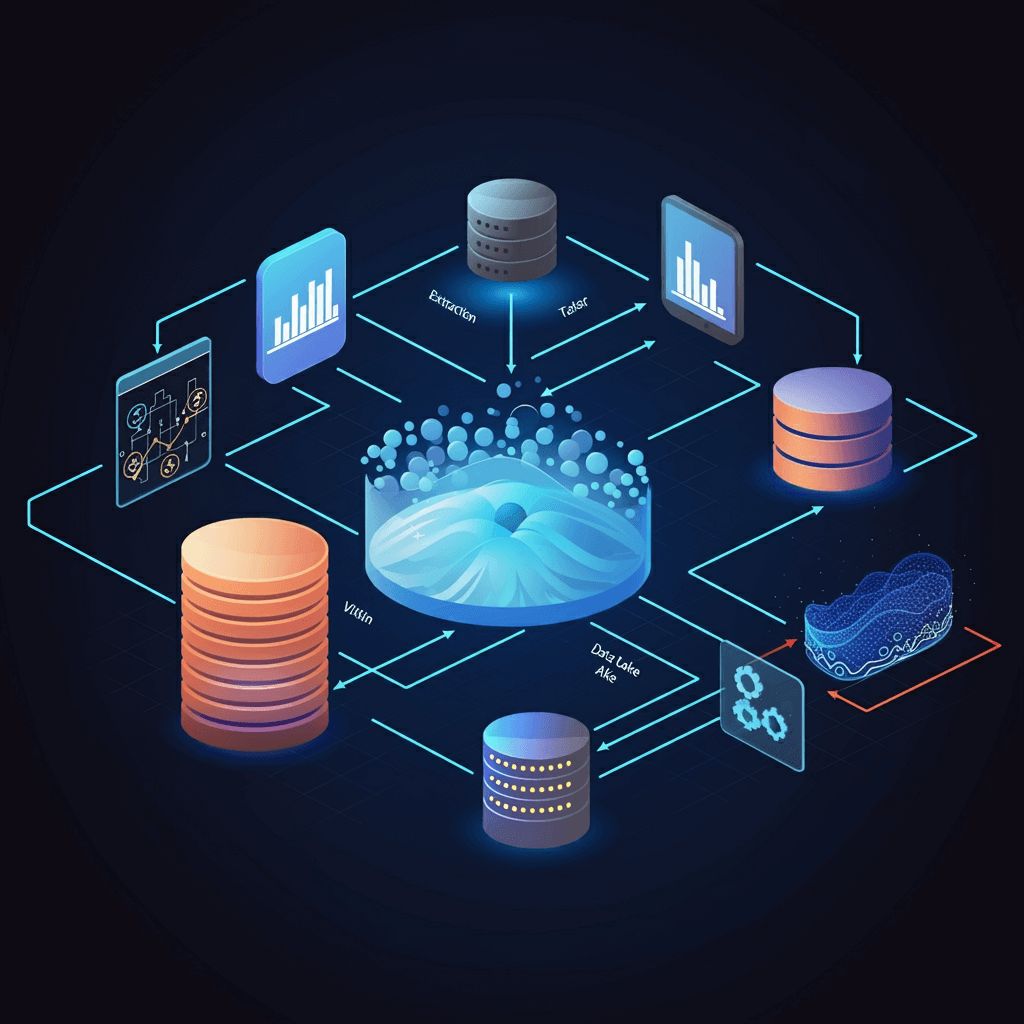
DCMM security essentially focuses on safeguarding data integrity and controlling access during the whole modernization phase. Automation, on the other hand, employs sophisticated technologies to simplify and ensure accuracy throughout migration efforts. These components are vital in creating a secure and efficient system that meets todays regulatory demands and complex data landscapes.
Solix advanced solutions, such as the Solix Common Data Platform (CDP) and Solix Enterprise Data Management Suite (ECS), are designed to support these DCMM initiatives. By integrating these tools, companies can optimize data governance and automate compliance in ways that also cater to operational needs, driving both performance and security.
Lets consider a hypothetical scenario where a complex organization, similar to those in regulated industries like finance or healthcare, is struggling with the enormity of their data migration project. Theyre facing significant challenges in managing vast amounts of sensitive data while also trying to adhere to strict compliance laws. Implementing DCMM solutions like those provided by Solix could significantly streamline their processes, improve security, and reduce the likelihood of data breaches.
For example, by adopting Solix ECS, such an organization could enjoy automated data lifecycle management, ensuring that every piece of data is accounted for, securely handled, and correctly archived or deleted according to legal requirements. This not only boosts security but also enhances operational efficiency, reducing both time and cost burdens associated with manual data handling.
Reflecting on a personal experience, I remember working with a client who was in the midst of transitioning their data systems to a more modern infrastructure. The complexities and risks involved were immense, given the sensitive nature of the data. Through the application of Solix ECS, we were able to automate critical segments of the migration, significantly decreasing the risk of human error and ensuring a smoother, faster process.
The real-world applications of DCMM in improving data governance and compliance are also endorsed by industry experts. A study by a well-regarded academic in the field, Dr. Li, indicated that organizations lagging in adopting DCMM security and automation face higher risks of data breaches and compliance penalties.
From my over a decade of expertise as a blogger at Solix, specializing in DCMM security and automation, Ive seen firsthand how implementing such technologies can propel organizations toward more innovative and efficient operational dynamics. My background, with a Computer Science degree from Michigan State University and years spent developing hypercomputing technologies, has provided me with insights that reinforce the transformative impact of DCMM processes backed by solutions like those offered by Solix.
In summary, transitioning to robust DCMM systems using platforms like Solix CDP and ECS is not just a strategic move but a necessary evolution for businesses operating in todays digital economy. It ensures not only compliance and data security but sets a foundation for future technological adoptions and data management enhancements.
If youre ready to take the plunge into optimized DCMM security and automation, dont hesitate to reach out. Explore our offerings, schedule a demo, or consult with our experts by calling 1-888-GO-SOLIX or visiting our contact pageAdditionally, dont miss the chance to WIN $100 by signing up for more information about these solutions, and see firsthand how they can transform your data management practices.
Join our giveaway now! Sign up to learn more about SOLIX solutions and enter for a chance to win a $100 gift card. Remember, our offer ends soon, so make sure to take action today!
About the Author
Sam is a senior technology writer at Solix.com, with over ten years of experience specializing in DCMM security and automation. His extensive background in computer science and hypercomputing technologies allows him to offer unique insights into data management sophistication, significantly aiding organizations in navigating the complexities of modern data environments.
This blog reflects the personal opinions of the author and not necessarily those of Solix Technologies.
Sign up now on the right for a chance to WIN $100 today! Our giveaway ends soon‚ dont miss out! Limited time offer! Enter on right to claim your $100 reward before its too late!
DISCLAIMER: THE CONTENT, VIEWS, AND OPINIONS EXPRESSED IN THIS BLOG ARE SOLELY THOSE OF THE AUTHOR(S) AND DO NOT REFLECT THE OFFICIAL POLICY OR POSITION OF SOLIX TECHNOLOGIES, INC., ITS AFFILIATES, OR PARTNERS. THIS BLOG IS OPERATED INDEPENDENTLY AND IS NOT REVIEWED OR ENDORSED BY SOLIX TECHNOLOGIES, INC. IN AN OFFICIAL CAPACITY. ALL THIRD-PARTY TRADEMARKS, LOGOS, AND COPYRIGHTED MATERIALS REFERENCED HEREIN ARE THE PROPERTY OF THEIR RESPECTIVE OWNERS. ANY USE IS STRICTLY FOR IDENTIFICATION, COMMENTARY, OR EDUCATIONAL PURPOSES UNDER THE DOCTRINE OF FAIR USE (U.S. COPYRIGHT ACT § 107 AND INTERNATIONAL EQUIVALENTS). NO SPONSORSHIP, ENDORSEMENT, OR AFFILIATION WITH SOLIX TECHNOLOGIES, INC. IS IMPLIED. CONTENT IS PROVIDED "AS-IS" WITHOUT WARRANTIES OF ACCURACY, COMPLETENESS, OR FITNESS FOR ANY PURPOSE. SOLIX TECHNOLOGIES, INC. DISCLAIMS ALL LIABILITY FOR ACTIONS TAKEN BASED ON THIS MATERIAL. READERS ASSUME FULL RESPONSIBILITY FOR THEIR USE OF THIS INFORMATION. SOLIX RESPECTS INTELLECTUAL PROPERTY RIGHTS. TO SUBMIT A DMCA TAKEDOWN REQUEST, EMAIL INFO@SOLIX.COM WITH: (1) IDENTIFICATION OF THE WORK, (2) THE INFRINGING MATERIAL’S URL, (3) YOUR CONTACT DETAILS, AND (4) A STATEMENT OF GOOD FAITH. VALID CLAIMS WILL RECEIVE PROMPT ATTENTION. BY ACCESSING THIS BLOG, YOU AGREE TO THIS DISCLAIMER AND OUR TERMS OF USE. THIS AGREEMENT IS GOVERNED BY THE LAWS OF CALIFORNIA.
-
White Paper
Enterprise Information Architecture for Gen AI and Machine Learning
Download White Paper -
-
-




